Why are we continually surprised as one story after the next comes out about Big Tech spying on us? Regardless of privacy policies or Government action, it's only going to get worse. It's in Big Tech's DNA to spy on us, and the proliferation of IoT / smart home gadgets along with artificial intelligence (AI) algorithms are only going accelerate the problem.
Below is a listing of various spying incidents. We hope it will help drive home that our society has a big problem and make you think twice before you order your next connected device that's built to spy on you.
Google Settles $5 Billion Consumer Privacy Lawsuit
Alphabet's Google ... secretly tracked the Internet use of millions of people who thought they were doing their browsing privately.
... Google's analytics, cookies and apps let the Alphabet unit track their activity even when they set Google's Chrome browser to "Incognito" mode and other browsers to "private" browsing mode.
Google uses Gmail to track a history of things you buy — and it’s hard to delete
"Google saves years of information on purchases you’ve made, even outside Google, and pulls this information from Gmail."
Gmail does scan all emails, new Google terms clarify
"Google’s system scans the content of emails stored on Google’s servers as well as those being sent and received by any Google email account"
Google calls Nest's hidden microphone an 'error'
"Google's Nest Secure hub, the Nest Guard, had a microphone, but you wouldn't have known that from the specs or the company itself. "
Google Wi-Fi Data Capture Unethical, But Not Illegal
"Google ... intercepted the unencrypted data that businesses and individuals beamed through the air willy-nilly. The data was left in the middle of the street so to speak, and Google gathered it as it drove through collecting photographs."
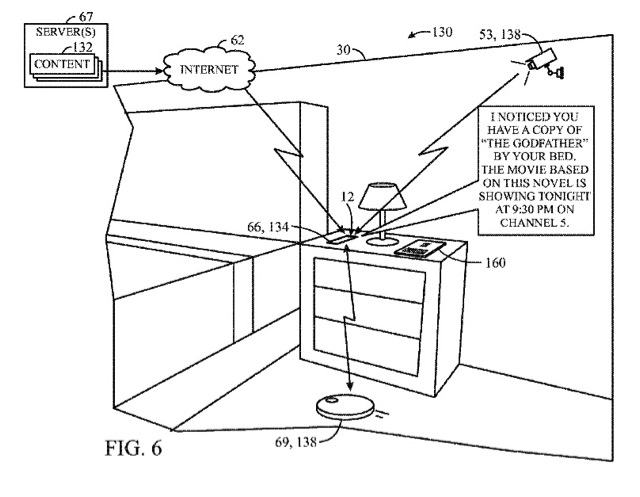
"A patent filed by the company suggests smart homes of the future could monitor naughtier members of the household with cameras, microphones, motion sensors and thermal imaging. The Google Home system could use this real-time information to decide if the person in question is misbehaving and needs telling off. In another patent Google described a device that would give advice to parents for 'areas of improvement' such as spending more time with their children at supper."
Google Home Mini Caught Spying on Users
"Some Google Home Mini units have been secretly recording just about every sound they hear and transmitting all of that information back to Google. While it's unclear what happens to the recordings once they land at Google, the obvious privacy implications are enough to scare just about anyone."
Alexa, Who has Access to my Data?
"... the processes used to handle personal data at amazon.de have serious issues. This is the “worst case scenario” that consumer and data protection activists have been warning us about."
"Alexa was obviously able to hear our ‘subject’ in the shower, and commands given to thermostats and the like showed that he uses Alexa to control various smart home appliances. He uses Alexa at home, on his smartphone, and when he is out and about."
"We were able to navigate around a complete stranger’s private life without his knowledge, and the immoral, almost voyeuristic nature of what we were doing got our hair standing on end. The alarms, Spotify commands, and public transport inquiries included in the data revealed a lot about the victims’ personal habits, their jobs, and their taste in music."
"The fact that Amazon linked a customer’s data to the wrong person and didn’t notice the mistake points to a severe lack of control over the processes involved. It is obvious that no serious checks took place."
NXP MCU Solution Enables Alexa Everywhere
"Soon, the newly emerging trend to build voice assistants directly into smart devices such as light switches, ceiling fans, appliances, smoke detectors, and thermostats, will make voice control ubiquitous throughout the home."
What is an Alexa Built-in Product?
If you're trying to avoid buying a product that let's Amazon listen in on your private life, then maybe the best place to start is Amazon's Alexa Built-In Storefront. Brands already in the Alexa Built-in Program include LG, First Alert, BOSE, Lenovo, Dell, and SONOS.
Company Accused of Spying on Customers Via Sex Toys
"A technology company selling vibrators uses a mobile application to spy on its customers in their most intimate moments..."
Dressing room 'booty cams' next step in store spying
"Some retail stores now have cameras in their dressing rooms... and can make instant stars out of the unsuspecting, you may want to ask if that camera feed is secure before turning your back on this latest retailing innovation."
Former employees say Lyft staffers spied on passengers
"Lyft staffers have been abusing customer insight software to view the personal contact info and ride history of the startup’s passengers."
Tracking Phones, Google Is a Dragnet for the Police
"The warrants, which draw on an enormous Google database employees call Sensorvault, turn the business of tracking cellphone users’ locations into a digital dragnet for law enforcement. In an era of ubiquitous data gathering by tech companies, it is just the latest example of how personal information — where you go, who your friends are, what you read, eat and watch, and when you do it — is being used for purposes many people never expected."
"Government agencies, courts, and parties in civil litigation regularly ask technology and communications companies to turn over user data."
The FBI Paid Geek Squad Employees as Informants
"The FBI has been in cahoots with Best Buy's Geek Squad for at least the past decade"
GPS and smartphone car technology raises questions about drivers' privacy
"We know everyone who breaks the law, we know when you're doing it. We have GPS in your car, so we know what you're doing ..."
"VIZIO facilitated appending specific demographic information to the viewing data, such as sex, age, income, marital status, household size, education level, home ownership, and household value ... VIZIO sold this information to third parties, who used it for various purposes..."
Samsung's warning: Our Smart TVs record your living room chatter
"Samsung's small print says that its Smart TV's voice recognition system will not only capture your private conversations, but also pass them onto third parties."
Verizon’s Super-Cookies Are Spying on You Right Now
"These programs ... let multiple companies track your online activities to identify the characteristics of those who would be most receptive to certain ads. You can opt out if you want, but Verizon will keep tracking your web browsing anyway, under the excuse of “other authentication purposes,” whatever that means."
Pennsylvania schools spying on students using laptop webcams, claims lawsuit
"A suburban Philadelphia school district remotely activates the cameras in school-provided laptops to spy on students in their homes ..."
Airbnb Has a Hidden-Camera Problem
"That was when he saw the light. Two small, black, rectangular boxes were stacked next to an outlet on the far side of the guest room, both facing the bed."
"What I’ve found since is that [the cameras] record to a memory card, but they can also stream live. The host could’ve been watching. Anybody could have been watching."
A woman is suing Airbnb over an alleged hidden camera
"On the third day of the trip, Schumacher noticed a light coming from behind some candles in the living room and discovered the camera. It was capable of audio recording and moved in response to various events, suggesting to Schumcher that it was being controlled remotely. "
A hidden camera was in their Airbnb bedroom. That’s for sex parties, owner tells cops
"A tiny black dot on the Longboat Key bedroom smoke detector was enough to alert an Indiana couple that something was wrong."
Smart electricity meters can be used to spy on private homes
"smart-meter technology ... allowed them to snoop on unencrypted data to determine whether or not the homeowners were home."
Google collects data on Android users’ locations even when location services are turned off
"A new report shows that Google has been accessing data about Android users’ locations, even when the user believes that the data is being kept private."
Facebook scraped call, text message data for years from Android phones
"While scanning the information Facebook had stored about his contacts, Dylan McKay discovered something distressing: Facebook also had about two years' worth of phone call metadata from his Android phone, including names, phone numbers, and the length of each call made or received."
Facebook reveals news feed experiment to control emotions
"It already knows whether you are single or dating, the first school you went to and whether you like or loathe Justin Bieber. But now Facebook, the world's biggest social networking site, is facing a storm of protest after it revealed it had discovered how to make users feel happier or sadder with a few computer key strokes."
The Big Hack: How China Used a Tiny Chip to Infiltrate U.S. Companies
"This attack was something graver than the software-based incidents the world has grown accustomed to seeing. Hardware hacks are more difficult to pull off and potentially more devastating, promising the kind of long-term, stealth access that spy agencies are willing to invest millions of dollars and many years to get."
"When a server was installed and switched on, the microchip altered the operating system’s core so it could accept modifications. The chip could also contact computers controlled by the attackers in search of further instructions and code."
The China SuperMicro Hack: About That Bloomberg Report
"This scheme is less crazy than it might seem. Modern circuit boards are filled with small support chips, and the backdoor chip would appear to be just another faceless component to all but the most detailed examination. "
"The attack reportedly focused on the Baseboard Management Controller (BMC), essentially a second small computer built into the server. The BMC implements the Intelligent Platform Management Interface, a tool enabling a remote administrator to reset the computer, reinstall the operating system, and perform other tasks without needing physical access."
WikiLeaks: The CIA is using popular TVs, smartphones and cars to spy on their owners
"... pieces of malware with names like “Assassin” and “Medusa” that seem drawn from a spy film, describing tools that the CIA uses to steal data from iPhones, seize control of Microsoft-powered computers or even make Internet-connected Samsung television sets secretly function as microphones."
Bruce Schneier: NSA Spying Is Making Us Less Safe
"The NSA’s actions are making us all less safe. They’re not just spying on the bad guys, they’re deliberately weakening Internet security for everyone—including the good guys. It’s sheer folly to believe that only the NSA can exploit the vulnerabilities they create."
Some concluding remarks
Regardless of privacy policies and Government legislation, spying & hacking are only going to get worse as connected systems continue to proliferate and become more complex. Combine this with the improvement and roll out of artificial intelligence that is used to data mine & classify, and we have an epic problem of privacy invasion.
However, all is not lost, and there is no reason to surrender to Big Tech's plan to spy on us. Your best defense today is to begin with the following plan of action:
- Learn about how the Internet is a shared, unsecure medium. For starters, know the difference between https and http, an address vs. a port, and why VPN isn't a panacea.
- Don't have an expectation of privacy with data you store in the cloud (e.g., pictures, email, video, etc.).
- Tell your vendors and suppliers to turn off (third party) tracking.
- Throw out devices that enable spying, or sell them to people you don't like.
- Think twice before you buy your next connected device and then save a few bucks by not buying it.



